Various Cisco Location Identifier Separation Protocol (LISP) operational components and processes are essential for LISP to function properly. These LISP protocol components include the following:
- Map Registration and Map Notify
- Map Request and Map Reply
- LISP Protocol Data Path
- Proxy ETR
- Proxy ITR
Map Registration and Notification
During the LISP setup, the ETR routers should be configured with the Endpoint Identifiers inside the LISP sites that are going to be advertised on the MS. All the subnets that are attached to the ETR that has no Endpoint Identifier (EID) prefixes configured shall be forwarded in a traditional way of routing.
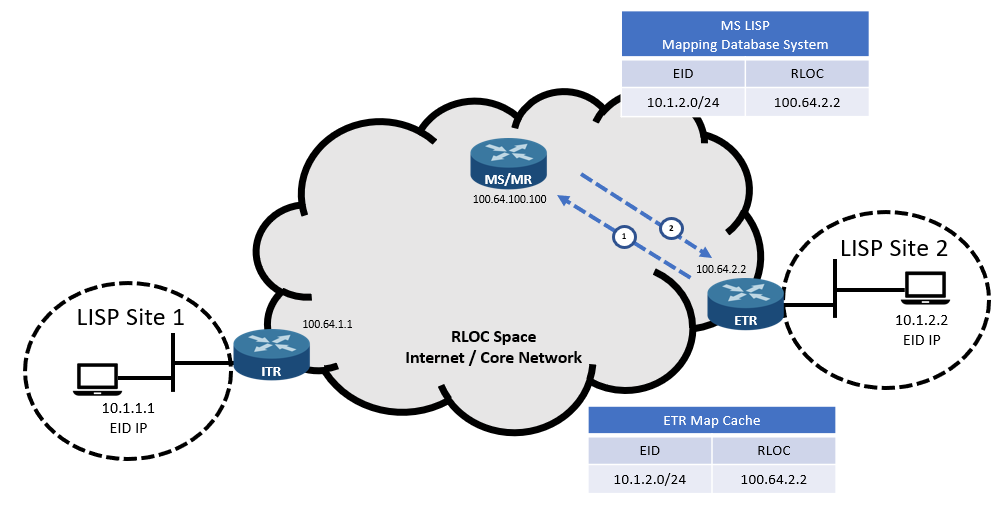
The map registration process includes the following steps:
- The Egress Tunnel Router (ETR) sends a “Map Register Message” to the Map Server (MS) router to register a new EID network, 10.1.2.0/24. The message also contains the router’s Routing Locator (RLOC) address, 100.64.2.2.
- The MS router sends back a “Map Notify Message” via the UDP port 4342, confirming that the EID network has been added to the database.
Map Request and Map Reply
For an endpoint inside and outside the LISP site to communicate, proper traffic routing should be configured first.
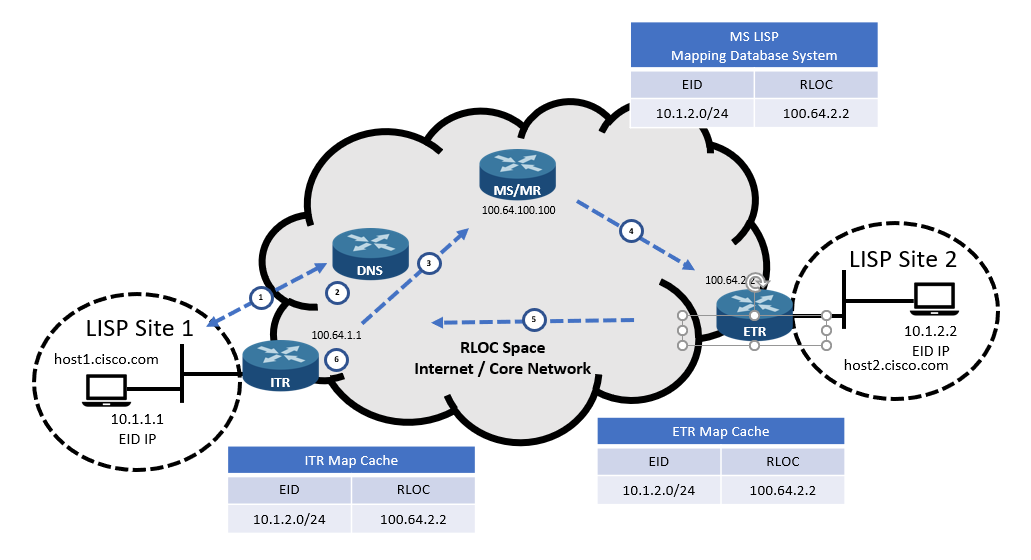
After reaching the Ingress Tunnel Router (ITR), the map request and reply process starts:
- The host from Site 1, host1, sends a DNS query to resolve the IP address of host2.cisco.com. The DNS server responds with the EID IP address 10.1.2.2. Then, host1 sends traffic to 10.1.2.2, but it will be forwarded to its default gateway (ITR).
- The ITR receives the packet directed to the address 10.1.2.2 and then performs the following verification:Does the packet match the default route because there is no other route for it?
- YES – The router goes to the next step.
- NO – The router follows a suitable routing route.
Is Source IP Address Registered EID Prefix in Local Cache?
- YES – The router goes to the next step.
- NO – The router forwards the packet natively.
- The ITR sends an encapsulated “Map Request” to the Map Resolver (MR) router regarding the address 10.1.2.2. The ITR selects the source port, and the destination port is UDP port 4342.
- If the MR router also acts as an MS router, the Map Request is redirected to the correct ETR destination router. However, if two independent devices perform these functions, the MR router will send a Map Request to the MS router, redirecting it to the correct ETR destination router.
- The ETR router sends a “Map Reply” response to the ITR, containing the EID-to-RLOC mapping (10.1.2.2 -> 100.64.2.2). The ETR can also request the MS router to respond to the map request messages if the “Proxy Map Reply” flag in the map register message is set.
- The ITR router stores the EID-to-RLOC mapping in its database, reprogramming the contents of the FIB table.
LISP Protocol Data Path
After receiving the EID-to-RLOC mapping from the ETR router (or MS router), the ITR router is ready to exchange data between the end devices considering the contents of the LISP header and the IP packet as a whole.
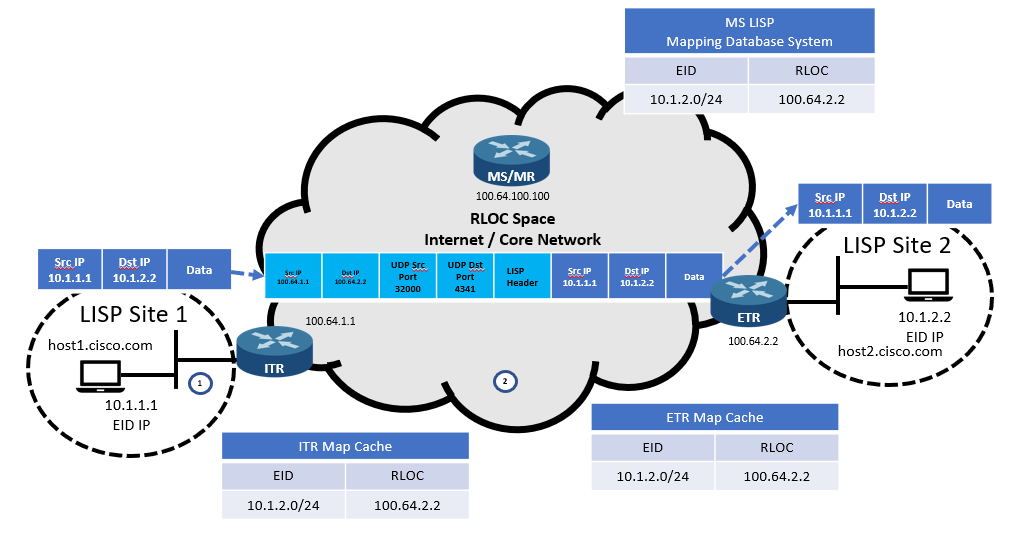
The process for LISP encapsulation and de-encapsulation is as follows:
- The ITR receives a packet from host1, 10.1.1.1, directed to host2, 10.2.2.2.
- The ITR finds a matching route in the FIB table, encapsulating the received EID packets with the ITR RLOC IP address as the source address and the ETR RLOC IP address as the destination address.
- The ETR router receives encapsulated IP packets. It then de-encapsulates it and forwards it to the destination address.
Proxy ETR (PETR)
When connecting to non-LISP sites, PETR is used. It doesn’t enter EID addresses in the LISP mapping system database. Therefore, when the ITR router sends a map request, the mapping database system will give a “Negative Map Reply”. The ITR should be enabled to send traffic to the PETR’s RLOC when a Negative Map Reply is received. The ITR will then forward LISP-encapsulated IP packets to PETR.
The shortest prefix is calculated by the mapping database system for the non-LISP site. The prefix must match the destination but does not match any LISP EID. The prefix will be then attached to the Negative Map Reply before being added to the map cache and FIB. Now, the ITR can send the non-LISP prefix to the PETR.
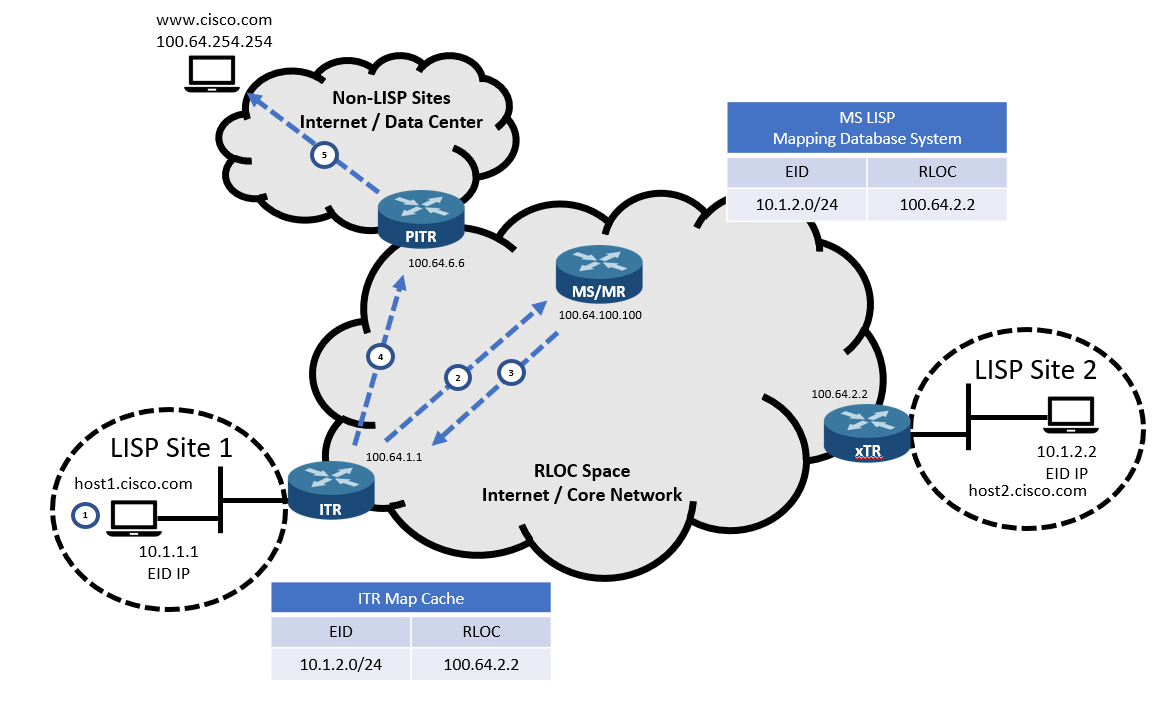
The Proxy ETR process has the following steps:
- Site 1’s host1 sends a DNS query for www.cisco.com, receiving the IP address 100.64.254.254 in response. It then sends the traffic to the ITR with the destination IP address 100.64.254.254.
- The ITR router sends a “Map Request” to the MR.
- The MR Router replies with a “Negative Map Reply” message containing the computed non-LISP route.
- The ITR router adds the received route to the FIB table and sends the encapsulated network traffic to the PETR.
- The PETR router de-encapsulates the received network traffic, sending it to www.cisco.com.
Proxy ITR (PITR)
PITRs receive the traffic from non-LISP sites which are sent to LISP EIDs. PITRs and ITRs act similarly. The only difference is that even if the source is not a registered EID, PITR sends “Map Request” messages to the MR.
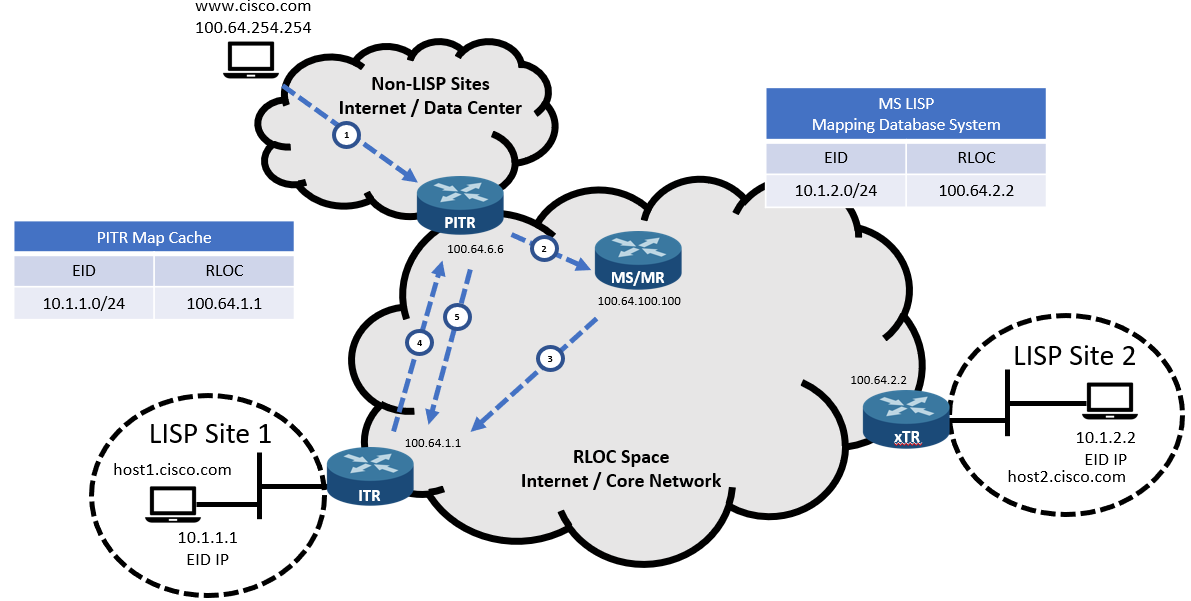
The Proxy ITR process includes the following steps:
- The PITR router receives incoming traffic from www.cisco.com to 10.1.1.1.
- The PITR sends a “Map Request” to the MR router.
- The mapping database system sends a “Map Request” to the ETR Router.
- The ETR router replies with the “Map Reply” message to the PITR, including the EID-to-RLOC mapping (10.1.1.1 -> 100.64.1.1).
- The PITR router encapsulates the network traffic and sends them to the ETR router.
- The ETR router de-encapsulates the received network traffic and forwards them to host1.
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training:
