The Cisco SAFE uses the Cisco Security Control Architecture (SCF), a common framework for selecting products and services that enhance visibility and control, the two most important security aspects. It also implements a security baseline that incorporates best practices for a secure network design. In addition, the architecture, which Cisco’s Continuous Improvement Lifecycle also utilizes, makes it easier to integrate Cisco’s extensive portfolio of security services designed to support the whole solution lifecycle.
Cisco SAFE PINs
Cybersecurity threats are constantly evolving, and there is no specific solution or product available that can protect organizations from all threats. To mitigate the problem, Cisco Systems introduced Cisco SAFE to help in the development of security services and solutions for the following places in the network (PINs):
Branch
The branch PINs are usually less secure compared with campus and data center PINs since branches are greater in number. Therefore, implementing all of the security features used in campus and data center PINs would be costly, making them perfect candidates for security breaches.
Endpoint malware, wireless infrastructure vulnerabilities, unauthorized and malicious client activity, and trust exploitation are among the most severe threats to branch PINs.
Campus
Campuses accommodate a large number of users, including personnel, guests, etc. Phishing, web-based exploits, unauthorized network access, malware distribution, and botnet attacks are prevalent on campus PINs.
Data Center
Data centers are the primary focus of all targeted threats because they store an organization’s most valuable information assets and intellectual property. In addition, a data center can have thousands of servers. In data centers, servers are typical, making it hard to install and maintain adequate security policies to regulate network access.
In data centers, common threats include data acquisition, malware distribution, unauthorized network access, botnet infections, data loss, backdoors, and reconnaissance.
Edge
The Internet edge is the most critical PIN since it is the primary entrance and exit point for traffic to and from the Internet. Some edge threats are web server vulnerabilities, DDoS attacks, data loss, and Man-in-the-Middle attacks.
Cloud
Service-level agreements (SLAs) with cloud service providers mandate cloud security and necessitates independent certification audits and risk assessments. The main cloud threads include web server vulnerabilities, loss of data and access, malware, and Man-in-the-Middle attacks.
Wide Area Network (WAN)
The WAN links all of the PINs. Managing WAN security can be very difficult, especially with hundreds of branches. The typical WAN threats are unauthorized network access, WAN sniffing, malware propagation, and Man-in-the-Middle attacks.
Cisco SAFE Secure Domains
The secure domains are the operational areas used to safeguard the various PINs. Each PIN is evaluated using the following security concepts:
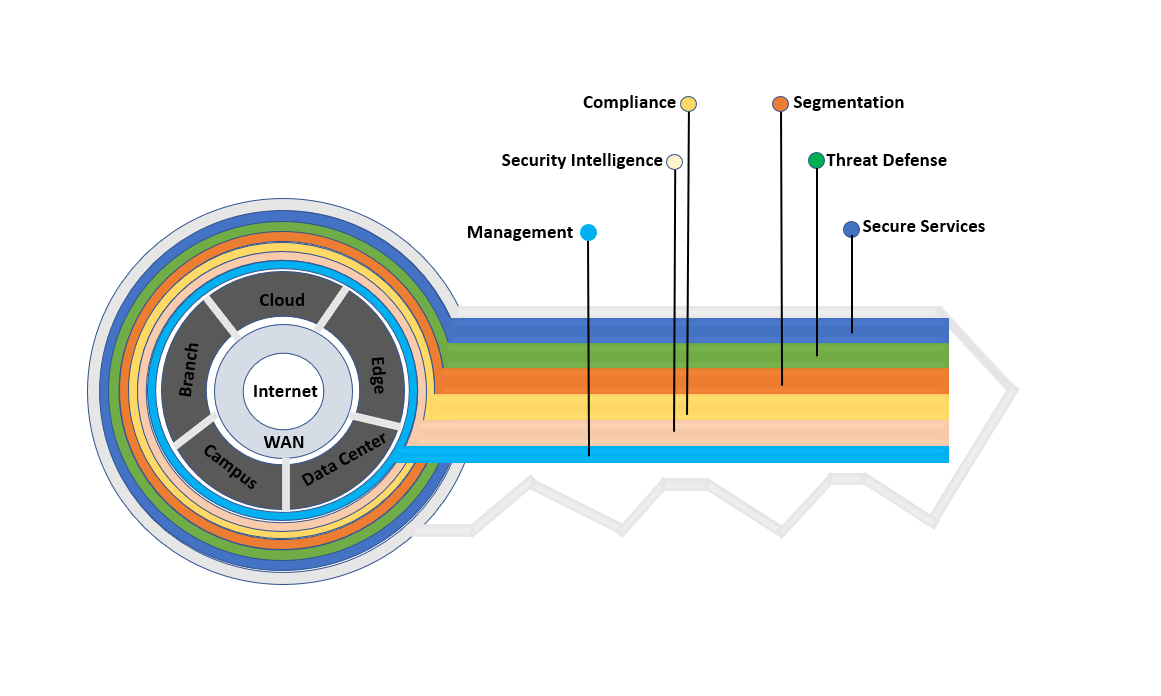
- Management – coordinates policies, objects, and alerts. It uses centralized services to manage workflow changes, policy deployments, and patching systems.
- Security Intelligence – used to detect malware and emerging threats. It also allows dynamic policy enforcement for accurate and appropriate security.
- Compliance – PINs must comply with security requirements such as PCI DSS 3.0 and HIPAA.
- Segmentation – defines data and user boundaries. Traditional manual segmentation employs network addresses and VLANs for policy enforcement, while advanced segmentation incorporates identity-aware infrastructure.
- Threat Defense – provides cyber threat visibility through network traffic telemetry, file reputation, and contextual data. It assesses the nature and possible risk of suspicious activities to respond appropriately to cyber threats.
- Secure Services – include Virtual Private Networks (VPNs), access control, and encryption. The security services also enable protection against insecure services through various methods such as authentication and authorization to secure access.
Threat Protection
The Cisco SAFE framework is modular. When the Cisco SAFE design architecture is implemented in an organization, it delivers enhanced threat defense protection for all PINs across the entire attack continuum: before, during, and after an attack.
Before an Attack
The threats and assets to be protected are identified in this phase. It also includes the establishment of policies and the implementation of risk-reduction measures.
Solutions: Next-generation firewalls, Network Access Control (NAC), network security analysis, and identity services.
During an Attack
The activities and actions taken are identified in this phase if an attack successfully gets through the network. The common actions taken include threat analysis and incident response.
Solutions: Malware protection, next-generation Intrusion Prevention System (IPS), next-generation firewalls, and email and online security solutions.
After an Attack
This phase includes detecting, scoping, containing, monitoring, and remediating the attack. The learnings from the successful attack are incorporated into the existing security solution.
Solutions: Cisco Advanced Malware Protection, next-generation firewalls, and Cisco Stealthwatch.
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training:
